Embark on a journey into the realm of Cybersecurity Solutions for Cloud Environments, where the security of data in the cloud takes center stage.
Delve into the intricacies of safeguarding sensitive information in cloud platforms and explore effective solutions to combat cyber threats.
Overview of Cybersecurity Solutions for Cloud Environments
Cybersecurity in cloud environments is of utmost importance due to the sensitive nature of the data stored and processed in the cloud. As more businesses and individuals migrate to cloud platforms for storage and computing needs, the risk of cyber threats also increases. It is crucial to implement robust cybersecurity solutions to protect data integrity, confidentiality, and availability in cloud environments.
Common Threats Faced by Cloud Systems
- Data Breaches: Unauthorized access to sensitive information stored in the cloud.
- Malware Infections: Viruses, ransomware, and other malicious software that can disrupt operations and steal data.
- DDoS Attacks: Distributed Denial of Service attacks that overwhelm cloud servers, causing downtime and service disruptions.
- Insider Threats: Malicious or negligent actions by authorized users leading to data leaks or breaches.
Challenges of Securing Data in Cloud Environments
- Shared Responsibility Model: Cloud providers and users share the responsibility of securing data, leading to potential gaps in protection.
- Compliance Issues: Meeting regulatory requirements and industry standards for data security in the cloud can be complex.
- Data Encryption: Ensuring data is encrypted both in transit and at rest to prevent unauthorized access.
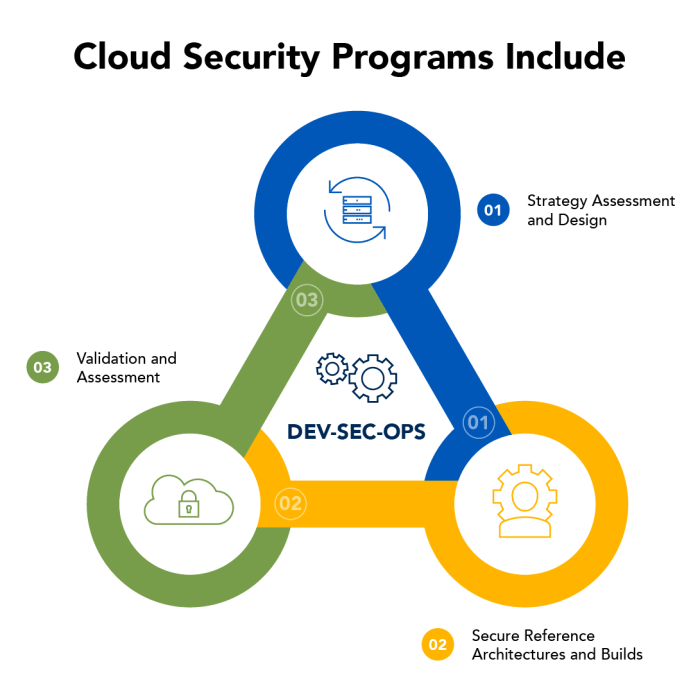
Successful Cybersecurity Solutions for Cloud Platforms
- Multi-Factor Authentication (MFA): Adding an extra layer of security by requiring multiple forms of verification for access.
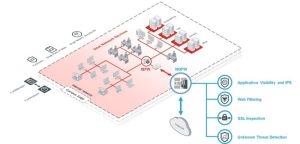
- Network Monitoring: Constantly monitoring network traffic for suspicious activity or potential security breaches.
- Endpoint Security: Protecting devices connected to the cloud from malware and other cyber threats.
- Security Information and Event Management (SIEM): Centralized logging and analysis of security events for proactive threat detection.
Implementation of Cybersecurity Measures in Cloud Environments
When it comes to implementing cybersecurity measures in cloud environments, it is essential to follow best practices to ensure the security of your infrastructure and data.
Securing Cloud Infrastructure and Data
Securing cloud infrastructure and data involves a combination of technical controls and best practices to prevent unauthorized access and data breaches.
- Regularly update and patch all systems and software to address security vulnerabilities.
- Implement strong access controls and regularly review and manage user permissions.
- Use encryption to protect data both in transit and at rest.
- Utilize network segmentation to isolate sensitive data and limit potential attack surfaces.
- Implement data loss prevention (DLP) solutions to monitor and prevent unauthorized data exfiltration.
The Role of Encryption in Safeguarding Cloud Data
Encryption plays a crucial role in safeguarding cloud data by converting plaintext information into ciphertext that can only be decrypted with the appropriate key.
- Use strong encryption algorithms to protect data both in transit and at rest.
- Implement encryption key management practices to securely store and manage encryption keys.
- Regularly rotate encryption keys to mitigate the risk of unauthorized access.
Multi-Factor Authentication in Cloud Environments
Multi-factor authentication (MFA) enhances security in cloud environments by requiring users to provide multiple forms of verification before granting access to sensitive data or resources.
- Implement MFA for all user accounts to add an extra layer of security beyond passwords.
- Utilize biometric authentication, one-time passcodes, or hardware tokens as additional factors for authentication.
- Regularly review and update MFA policies to align with evolving security threats and best practices.
Role of Data Analytics in Cybersecurity Solutions

Data analytics plays a crucial role in enhancing cybersecurity measures, especially in cloud environments. By analyzing vast amounts of data, organizations can detect and prevent cyber threats proactively, rather than reactively. This proactive approach is essential in mitigating risks and protecting sensitive information stored in the cloud.
Significance of Data Analytics in Cybersecurity
- Data analytics helps in identifying patterns and anomalies in network traffic, enabling early detection of potential threats.
- By leveraging machine learning algorithms, data analytics can continuously learn from new data and adapt to evolving cyber threats.
- Real-time monitoring and analysis of data allow for immediate response to security incidents, reducing the impact of breaches.
Machine Learning Algorithms for Cybersecurity in Cloud Environments
- Machine learning algorithms can analyze large datasets to identify malicious activities, such as unauthorized access or data exfiltration.
- These algorithms can also predict potential security breaches based on historical data, helping organizations take preventive actions.
- Automated response systems powered by machine learning can enhance incident response capabilities and reduce manual intervention.
Data Analytics Tools for Cybersecurity Monitoring
- Security Information and Event Management (SIEM) tools aggregate and correlate data from various sources to detect security incidents.
- User and Entity Behavior Analytics (UEBA) tools analyze user behavior to identify suspicious activities and potential insider threats.
- Network Traffic Analysis (NTA) tools monitor network traffic for anomalies and malicious patterns, enhancing threat detection capabilities.
Leveraging Data Analytics for Real-Time Threat Detection
- By integrating data analytics tools with cloud security platforms, organizations can monitor their cloud environments in real-time for security threats.
- Continuous monitoring and analysis of logs, events, and user activities enable quick identification of security incidents.
- Automated alerts and responses based on data analytics help in mitigating cyber threats before they escalate, ensuring the security of cloud data and applications.
In conclusion, Cybersecurity Solutions for Cloud Environments play a pivotal role in ensuring the integrity and confidentiality of data stored in the cloud, highlighting the importance of robust security measures in today’s digital landscape.
User Queries
How can encryption enhance cloud data security?
Encryption plays a crucial role in protecting data by encoding it into an unreadable format, ensuring that only authorized users can access sensitive information.
What are the best practices for securing cloud infrastructure?
Implementing strong access controls, regular security audits, and continuous monitoring are essential best practices for securing cloud infrastructure.
How does data analytics contribute to cybersecurity in cloud environments?
Data analytics helps in detecting anomalies and patterns that indicate potential cyber threats, enabling proactive measures to enhance security in cloud environments.