Endpoint protection is paramount in today’s complex threat landscape. This guide delves into the crucial aspects of securing endpoints, exploring various solutions, deployment strategies, and advanced capabilities. We’ll examine how different technologies, from traditional antivirus to cutting-edge EDR, work to protect against evolving cyber threats and the importance of integrating these solutions into a broader cybersecurity framework. Understanding endpoint protection is no longer optional; it’s a necessity for organizations of all sizes.
We’ll cover a range of topics, from defining core functionalities and comparing different solution types to managing deployments across networks and integrating with other security tools. We’ll also discuss future trends and the impact of emerging technologies on endpoint security strategies, offering practical insights and best practices to bolster your organization’s defenses.
Cybersecurity Solutions

Endpoint protection is a crucial first line of defense, but a robust cybersecurity strategy requires a multi-layered approach encompassing various solutions working in concert. A holistic strategy considers the interconnectedness of different systems and data, acknowledging that a breach in one area can compromise the entire organization. This section explores the broader landscape of cybersecurity solutions and their synergistic relationship.
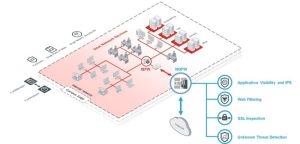
Effective cybersecurity relies on a layered security model, where multiple solutions work together to protect against a wide range of threats. Endpoint protection forms a vital base layer, securing individual devices. However, this needs to be complemented by other layers addressing network vulnerabilities, cloud-based data, and the overall security posture of the organization’s data assets.
The Interplay Between Cybersecurity Domains
Endpoint protection, while essential, is only one piece of the puzzle. Network security safeguards the infrastructure connecting these endpoints, preventing unauthorized access and malicious traffic. Cloud security protects data and applications stored in the cloud, mitigating risks associated with cloud storage and services. Data security focuses on protecting sensitive information regardless of its location—on endpoints, in the network, or in the cloud.
These domains are deeply interconnected; a compromised endpoint can lead to a network breach, which could then expose cloud-based data. For example, a phishing email targeting an employee’s endpoint could lead to malware installation, allowing attackers to move laterally through the network and access sensitive data stored in the cloud. A layered approach, combining robust endpoint protection with strong network, cloud, and data security measures, significantly reduces the likelihood and impact of successful attacks.
Categories of Cybersecurity Solutions
A comprehensive cybersecurity strategy incorporates various solutions across multiple categories. Understanding their functions is crucial for building an effective defense.
The following list Artikels several key categories and their primary functions:
- Endpoint Protection: This includes antivirus software, firewalls, intrusion detection/prevention systems (IDS/IPS), data loss prevention (DLP) tools, and endpoint detection and response (EDR) solutions. These tools protect individual devices from malware, unauthorized access, and data breaches.
- Network Security: This encompasses firewalls, intrusion detection/prevention systems (IDS/IPS), virtual private networks (VPNs), and network segmentation. These solutions protect the organization’s network infrastructure from unauthorized access and malicious traffic.
- Cloud Security: This includes cloud access security brokers (CASBs), cloud security posture management (CSPM) tools, and cloud workload protection platforms (CWPPs). These tools protect data and applications stored in the cloud environments.
- Data Security: This involves data encryption, access control, data loss prevention (DLP), and data masking. These measures protect sensitive data regardless of its location.
- Identity and Access Management (IAM): This involves authentication, authorization, and single sign-on (SSO) solutions. IAM systems control user access to resources, preventing unauthorized access.
- Security Information and Event Management (SIEM): SIEM systems collect and analyze security logs from various sources to detect and respond to security incidents.
- Vulnerability Management: This involves identifying and mitigating vulnerabilities in systems and applications. Regular vulnerability scanning and patching are crucial components.
Effective endpoint protection is a multifaceted challenge demanding a layered and integrated approach. By understanding the core functionalities of various solutions, implementing robust deployment strategies, and integrating with broader cybersecurity frameworks, organizations can significantly mitigate risks and protect their valuable data. Staying informed about emerging threats and leveraging advancements in AI and machine learning will be crucial in maintaining a strong security posture in the ever-evolving landscape of cyber threats.
Proactive and adaptable security strategies are key to successful endpoint protection.
Questions Often Asked
What is the difference between antivirus and anti-malware?
Antivirus software primarily focuses on detecting and removing known viruses, while anti-malware software has a broader scope, encompassing various threats beyond viruses, such as worms, Trojans, and spyware.
How often should endpoint protection software be updated?
Endpoint protection software should be updated automatically as frequently as possible. Many solutions provide automatic updates; ensure this feature is enabled.
What is the role of sandboxing in endpoint protection?
Sandboxing isolates suspicious files or programs in a virtual environment to analyze their behavior without risking the main system. This allows for safe evaluation of potentially malicious code.
Is endpoint protection enough to ensure complete security?
No, endpoint protection is a crucial component, but it’s part of a layered security strategy. Network security, data security, and user education are equally vital.