In today’s digital age, the need for robust cybersecurity solutions in enterprises has never been more critical. As cyber threats continue to evolve, it is imperative for businesses to stay ahead of the curve by implementing effective security measures. Let’s delve into the world of Enterprise Cybersecurity Solutions to explore how organizations can fortify their defenses and protect sensitive data.
Overview of Enterprise Cybersecurity Solutions

Cybersecurity solutions are crucial for enterprises to protect their sensitive data, systems, and networks from cyber threats. As technology advances, so do the tactics of cybercriminals, making it essential for businesses to implement robust cybersecurity measures.
Importance of Cybersecurity Solutions for Enterprises
Implementing cybersecurity solutions in an enterprise setting is vital to safeguarding valuable assets and maintaining the trust of customers and stakeholders. Without adequate protection, companies are at risk of data breaches, financial losses, and reputational damage.
Main Objectives of Implementing Cybersecurity Solutions
- Protecting sensitive data: Ensuring that confidential information is secure from unauthorized access or theft.
- Preventing cyber attacks: Implementing measures to detect and thwart potential threats before they cause harm.
- Maintaining compliance: Adhering to industry regulations and standards to avoid legal consequences.
Common Cybersecurity Threats Faced by Enterprises
- Phishing attacks: Deceptive emails or messages used to trick employees into revealing sensitive information.
- Ransomware: Malicious software that encrypts data and demands payment for its release.
- Insider threats: Employees or contractors who misuse their access to compromise security.
Types of Enterprise Cybersecurity Solutions
In the realm of enterprise cybersecurity, there are several types of solutions designed to protect organizations from cyber threats. Each type offers specific functions and features to enhance security measures within an enterprise environment. Let’s delve into the various types of cybersecurity solutions tailored for enterprises.
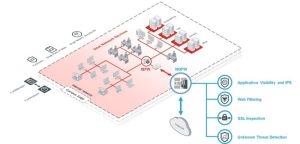
Firewalls
Firewalls act as a barrier between a trusted internal network and untrusted external networks, filtering incoming and outgoing network traffic based on a set of security rules. They help prevent unauthorized access to or from private networks and can be implemented as hardware, software, or a combination of both.
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
IDS monitors network traffic for suspicious activity or known malicious patterns, while IPS goes a step further by actively blocking or preventing such activity. These systems help detect and respond to potential security breaches in real-time, providing an additional layer of defense against cyber threats.
Endpoint Security
Endpoint security solutions focus on securing individual devices such as laptops, smartphones, and tablets connected to the corporate network. They protect endpoints from malware, data theft, and unauthorized access, ensuring that each device meets the organization’s security standards.
Data Loss Prevention (DLP)
DLP solutions aim to prevent the unauthorized transfer of sensitive data outside the organization. By monitoring and controlling data in motion, at rest, and in use, DLP tools help organizations safeguard their valuable information and maintain compliance with data protection regulations.
Identity and Access Management (IAM)
IAM solutions manage user identities and their access rights to enterprise resources. By implementing strong authentication, authorization, and access control policies, IAM helps organizations ensure that only authorized individuals can access sensitive data and systems, reducing the risk of insider threats.
Security Information and Event Management (SIEM)
SIEM solutions collect, analyze, and correlate security event data from various sources across the enterprise. By providing real-time visibility into security incidents and trends, SIEM helps organizations detect and respond to cyber threats more effectively, enhancing overall security posture.
Cloud Security
As more enterprises adopt cloud services, cloud security solutions become essential to protect data and applications hosted in the cloud. These solutions offer encryption, access controls, and threat detection mechanisms to secure cloud environments and ensure data confidentiality and integrity.
Security Awareness Training
Educating employees about cybersecurity best practices is crucial in preventing human errors and vulnerabilities. Security awareness training programs help raise awareness about potential threats, phishing scams, and social engineering tactics, empowering employees to recognize and respond to security incidents proactively.
Implementation of Enterprise Cybersecurity Solutions

Implementing cybersecurity solutions within an enterprise is a crucial process to protect sensitive data and secure the organization’s digital assets. Here are the steps involved in implementing cybersecurity solutions, best practices for integration, and the role of policies and compliance regulations.
Steps in Implementing Cybersecurity Solutions
- Assessment of Current Security Measures: Conduct a thorough assessment of the existing security infrastructure to identify vulnerabilities and areas that need improvement.
- Develop a Comprehensive Security Strategy: Create a detailed plan outlining the specific cybersecurity solutions needed to address the identified risks and vulnerabilities.
- Selection of Security Solutions: Choose the right cybersecurity solutions that align with the organization’s security strategy and requirements.
- Implementation and Testing: Deploy the selected security solutions and conduct thorough testing to ensure they are effectively protecting the organization’s assets.
- Training and Awareness: Provide training for employees on cybersecurity best practices and raise awareness about the importance of cybersecurity within the organization.
- Continuous Monitoring and Updates: Regularly monitor the cybersecurity solutions in place, update them as needed, and stay informed about emerging threats.
Best Practices for Integration into Existing IT Infrastructure
- Align with Business Goals: Ensure that cybersecurity solutions are aligned with the overall business objectives and IT strategy of the organization.
- Collaboration with IT and Security Teams: Foster collaboration between IT and security teams to ensure seamless integration of cybersecurity solutions.
- Use of Standardized Protocols: Implement standardized protocols and best practices to ensure compatibility and interoperability within the existing IT infrastructure.
- Regular Security Audits: Conduct regular security audits to assess the effectiveness of the integrated cybersecurity solutions and identify any gaps or weaknesses.
Role of Cybersecurity Policies and Compliance Regulations
- Establishment of Policies: Develop and implement cybersecurity policies that Artikel the organization’s approach to cybersecurity, compliance requirements, and best practices.
- Compliance with Regulations: Ensure that the implemented cybersecurity solutions comply with relevant regulations, such as GDPR, HIPAA, or PCI DSS, to avoid legal and financial repercussions.
- Employee Training: Educate employees on cybersecurity policies and compliance regulations to ensure adherence and mitigate risks related to non-compliance.
Importance of Data Analytics in Cybersecurity Solutions
Data analytics plays a crucial role in enhancing cybersecurity measures for enterprises by providing valuable insights into potential threats and vulnerabilities. By analyzing vast amounts of data in real-time, organizations can proactively identify and mitigate security risks, safeguarding their sensitive information and digital assets.
Role of Data Analytics in Identifying and Mitigating Cybersecurity Threats
Data analytics tools and techniques are instrumental in identifying patterns and anomalies that could indicate a potential cyber attack. Through advanced algorithms and machine learning models, organizations can detect suspicious activities, unauthorized access attempts, and other security breaches in their network. By leveraging data analytics, cybersecurity professionals can respond promptly to threats, prevent data breaches, and strengthen their defense mechanisms.
- Behavioral Analytics: By analyzing user behavior and network traffic patterns, organizations can identify deviations from normal activities that may indicate a security threat.
- Threat Intelligence Platforms: These tools aggregate and analyze data from various sources to provide insights into emerging threats, vulnerabilities, and attack vectors.
- Security Information and Event Management (SIEM) Systems: SIEM solutions collect and analyze log data from across the IT environment to detect and respond to security incidents in real-time.
As we conclude our exploration of Enterprise Cybersecurity Solutions, it becomes evident that safeguarding business assets and information is paramount in today’s tech-driven landscape. By embracing cutting-edge security strategies and staying vigilant against emerging threats, enterprises can navigate the digital realm with confidence and resilience.
FAQs
How often should cybersecurity solutions be updated?
Cybersecurity solutions should be updated regularly to address new threats and vulnerabilities. It is recommended to update systems and software as soon as patches or updates are released.
What role do employee training programs play in enterprise cybersecurity?
Employee training is crucial in raising awareness about cybersecurity best practices and potential threats. By educating staff on how to identify and respond to security incidents, businesses can significantly enhance their overall security posture.
Are there any specific regulations that govern cybersecurity practices in enterprises?
Yes, there are various compliance regulations such as GDPR, HIPAA, and PCI DSS that mandate specific cybersecurity practices for handling sensitive data in enterprises. It is essential for organizations to adhere to these regulations to avoid potential legal consequences.