The rise of remote work has dramatically reshaped the modern workplace, offering flexibility and convenience. However, this shift has also introduced a new set of cybersecurity challenges. Remote employees, often working from unsecured networks or personal devices, face heightened risks of cyberattacks, data breaches, and other security vulnerabilities. Understanding and mitigating these risks is crucial for maintaining business continuity and protecting sensitive information.
This exploration delves into the multifaceted landscape of cybersecurity solutions designed to address the unique threats posed by remote work. We will examine essential security measures, best practices for data protection, and strategies for effective cybersecurity awareness training. The goal is to equip organizations and individuals with the knowledge and tools necessary to navigate the complexities of remote work security effectively and confidently.
Securing Remote Access to Corporate Networks
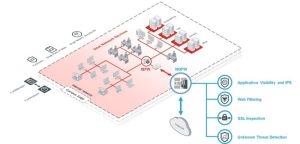
Securing remote access to corporate networks is paramount in today’s distributed work environment. A robust strategy safeguards sensitive data and maintains business continuity while enabling employees to work effectively from anywhere. This requires a multi-layered approach encompassing secure access methods, strong authentication, and comprehensive device management.
Effective remote access hinges on employing secure technologies and implementing stringent security policies. The primary methods for achieving this include Virtual Private Networks (VPNs) and Zero Trust Network Access (ZTNA). Both offer distinct advantages in protecting corporate resources, but their implementation and suitability vary depending on organizational needs and infrastructure.
VPN Implementation
A well-implemented VPN establishes a secure, encrypted connection between a remote device and the corporate network. This effectively extends the corporate network to the remote location, allowing employees to access internal resources as if they were physically present in the office. The implementation process involves several key steps:
Firstly, choosing the right VPN solution is crucial. Factors to consider include scalability, ease of management, support for various platforms, and security features. After selecting a VPN vendor, the next step involves configuring the VPN server on the corporate network. This includes setting up appropriate security protocols (like IPsec or OpenVPN), configuring access controls, and implementing strong authentication mechanisms.
Finally, user accounts need to be created and managed, ensuring each employee has the necessary permissions and access levels. Regular updates and security audits are essential to maintain the integrity and effectiveness of the VPN solution.
Zero Trust Network Access (ZTNA)
ZTNA represents a more granular and modern approach to secure remote access. Unlike VPNs, which provide broad network access once authenticated, ZTNA employs a “never trust, always verify” philosophy. Each access request is verified based on multiple factors, including user identity, device posture, and application context. This micro-segmentation approach limits access only to the specific resources required by the user, significantly reducing the attack surface.
ZTNA solutions often leverage cloud-based infrastructure and advanced authentication techniques, providing a highly secure and scalable solution for remote access.
Security Implications of Using Personal Devices
Using personal devices for accessing corporate networks introduces significant security risks. Personal devices are often less secure than corporate-managed devices, lacking robust endpoint protection, up-to-date software, and strong password policies. This increases the vulnerability to malware, phishing attacks, and data breaches. Furthermore, the lack of control over personal devices makes it difficult to enforce security policies and manage access effectively.
Organizations should implement robust mobile device management (MDM) solutions to mitigate these risks, ensuring personal devices meet minimum security standards before accessing corporate resources.
Secure Remote Access Guide for Employees
To ensure secure access to company resources from remote locations, employees should follow these steps:
- Only use the approved VPN client provided by the company.
- Ensure your operating system and applications are up-to-date with the latest security patches.
- Use a strong, unique password for your VPN account and adhere to the company’s password policy.
- Avoid using public Wi-Fi networks whenever possible; if unavoidable, use a VPN to encrypt your connection.
- Be cautious of phishing emails and suspicious links; never share your VPN credentials or other sensitive information.
- Report any suspicious activity or security incidents immediately to the IT department.
- Familiarize yourself with the company’s security policies and procedures regarding remote access.
Data Security and Protection for Remote Workers

Securing data in a remote work environment presents unique challenges. The traditional perimeter-based security model is less effective when employees access corporate resources from various locations and devices. A robust strategy encompassing device security, data encryption, and robust data loss prevention measures is crucial to mitigating risks. This section Artikels key best practices for safeguarding sensitive information.
Securing Sensitive Data on Remote Devices and in Cloud Storage
Effective data security begins with securing the devices themselves. Strong passwords, multi-factor authentication (MFA), and regular software updates are fundamental. For sensitive data stored locally, full-disk encryption is highly recommended. This renders data unreadable without the correct decryption key, even if the device is lost or stolen. Cloud storage services should be carefully vetted, ensuring they meet the organization’s security requirements, including data encryption both in transit and at rest.
Data stored in the cloud should be segmented and access strictly controlled using role-based access controls (RBAC). Regular security audits and vulnerability scans are essential for both on-device and cloud-based data.
Data Loss Prevention (DLP) Strategies for Remote Work Environments
Data loss prevention strategies aim to prevent sensitive information from leaving the organization’s control. Implementing DLP tools that monitor data movement and usage is vital. These tools can scan for sensitive data within emails, files, and applications, preventing unauthorized access or transfer. Regular data loss prevention training for employees is crucial to reinforce best practices and highlight potential risks.
A clear data classification policy that categorizes data based on sensitivity level helps determine appropriate security controls and access restrictions. Implementing data usage monitoring and reporting capabilities enables proactive identification of potential data breaches or leaks.
The Role of Data Encryption in Protecting Sensitive Information
Data encryption is a cornerstone of data security. Encryption transforms data into an unreadable format, protecting it from unauthorized access. Encryption is crucial both during data transmission (in transit) and when data is stored (at rest). For data in transit, secure protocols like HTTPS and SFTP should be used. For data at rest, full-disk encryption for devices and robust encryption at the cloud storage level are necessary.
Choosing strong encryption algorithms and regularly updating encryption keys enhances security. The use of encryption keys should follow strict key management practices, including secure storage and regular rotation.
Securing Data Backups and Recovery Procedures for Remote Workers
Regular data backups are essential for business continuity and disaster recovery. Remote workers should have a clear process for backing up their data, ideally to multiple locations. This could involve cloud-based backup services, local backups to external drives, or a combination of both. The backup strategy should include versioning to allow recovery of previous versions of files.
Testing the backup and recovery process regularly is critical to ensure its effectiveness in case of an incident. A clear incident response plan should be in place, outlining the steps to take in case of data loss or a security breach, including procedures for data recovery and notification of affected parties.
Cybersecurity Awareness Training for Remote Employees
A comprehensive cybersecurity awareness training program is crucial for protecting a company’s data and reputation in the age of remote work. Remote employees often operate with less direct oversight, increasing their vulnerability to cyber threats. Effective training empowers them to recognize and mitigate these risks, minimizing the likelihood of successful attacks.Effective training goes beyond simply delivering information; it fosters a security-conscious culture within the remote workforce.
This involves engaging employees through interactive methods and relatable scenarios, ensuring the training is memorable and actionable. Regular reinforcement and updates are also vital, as threats and tactics constantly evolve.
Phishing Awareness Training
Phishing attacks remain a primary vector for cybercriminals targeting remote workers. Training should focus on identifying the common characteristics of phishing emails, such as suspicious sender addresses, urgent or threatening language, and unusual requests for personal information. Employees should be instructed on how to verify the authenticity of emails and websites before clicking on links or downloading attachments.
Real-world examples of successful phishing campaigns, highlighting the techniques used and the resulting consequences, can serve as powerful learning tools. For instance, a detailed case study of a phishing attack that compromised a company’s payroll system could demonstrate the significant financial and reputational damage that can result.
Password Security Best Practices
Strong and unique passwords are the first line of defense against unauthorized access. Training should emphasize the importance of creating complex passwords that combine uppercase and lowercase letters, numbers, and symbols. Employees should be discouraged from reusing passwords across multiple accounts and encouraged to utilize password managers to securely store and manage their credentials. The training should also address the risks associated with password sharing and the importance of immediately reporting any suspected compromise.
An example could involve demonstrating the ease with which a simple password can be cracked using readily available tools, contrasted with the significantly greater time and resources required to crack a complex password.
Social Engineering Tactics
Social engineering attacks exploit human psychology to gain access to sensitive information or systems. Training should cover various social engineering techniques, including pretexting, baiting, and quid pro quo. Employees should be taught to be skeptical of unsolicited requests, verify the identity of individuals requesting information, and understand the potential consequences of divulging sensitive data. A scenario could involve a simulated phone call from a supposed IT support representative attempting to obtain login credentials, illustrating how to identify and respond to such attempts.
The training could also include examples of real-world social engineering attacks targeting remote workers, analyzing the methods used and the resulting damage.
Cybersecurity Solutions
Effective cybersecurity is paramount in today’s interconnected world, especially for organizations embracing remote work models. A robust cybersecurity strategy requires a multifaceted approach, encompassing technological solutions, robust policies, and well-trained personnel. This section delves into the broader principles and considerations crucial for establishing a comprehensive cybersecurity posture.
Key Principles of Cybersecurity
Cybersecurity rests on several core tenets. Confidentiality ensures that sensitive information is accessible only to authorized individuals. Integrity maintains the accuracy and completeness of data, preventing unauthorized modification or deletion. Availability guarantees timely and reliable access to information and resources for authorized users. These three principles – often referred to as the CIA triad – form the foundation of any effective cybersecurity program.
Beyond the CIA triad, other crucial principles include non-repudiation (ensuring actions can be traced back to the responsible party) and authenticity (verifying the identity of users and devices). A holistic approach incorporating all these principles is essential for mitigating risks effectively.
Types of Cybersecurity Threats and Vulnerabilities
The cybersecurity landscape is constantly evolving, with new threats emerging regularly. Malware, encompassing viruses, worms, Trojans, and ransomware, poses a significant risk, capable of compromising systems, stealing data, and disrupting operations. Phishing attacks, designed to deceive users into revealing sensitive information, remain a prevalent threat vector. Denial-of-service (DoS) attacks overwhelm systems with traffic, rendering them unavailable to legitimate users.
Insider threats, stemming from malicious or negligent actions by employees or contractors, also present a considerable risk. Vulnerabilities arise from software flaws, weak passwords, insecure configurations, and inadequate security controls. Regular security assessments and patching are vital for identifying and mitigating these vulnerabilities. For example, a failure to update software can leave systems vulnerable to exploits, as seen in the widespread impact of the WannaCry ransomware attack.
Cybersecurity Frameworks and Standards
Several established frameworks provide guidance for building and managing effective cybersecurity programs. The National Institute of Standards and Technology (NIST) Cybersecurity Framework is a widely adopted framework that offers a flexible approach to managing cybersecurity risk. It consists of five core functions: Identify, Protect, Detect, Respond, and Recover. Each function Artikels specific activities and best practices to help organizations improve their cybersecurity posture.
Other relevant frameworks include ISO 27001, a widely recognized international standard for information security management systems, and the CIS Controls, a prioritized set of cybersecurity safeguards developed by the Center for Internet Security. These frameworks provide a structured approach to managing cybersecurity risk, helping organizations to align their efforts with industry best practices and regulatory requirements.
Incident Response and Recovery Approaches
Effective incident response and recovery are critical for minimizing the impact of cybersecurity incidents. Different approaches exist, ranging from reactive measures to proactive strategies. Reactive approaches focus on containing and mitigating incidents after they occur. This involves steps like isolating affected systems, analyzing the incident, and restoring data from backups. Proactive approaches emphasize prevention and preparedness, including regular security awareness training, penetration testing, and incident response planning.
A well-defined incident response plan, outlining roles, responsibilities, and procedures, is crucial for effective incident handling. The choice of approach depends on factors like the organization’s size, resources, and risk tolerance. For instance, a large organization might invest heavily in proactive security measures, while a smaller organization might focus on a more reactive approach, supplemented by robust insurance coverage.
Securing remote work environments requires a multifaceted approach encompassing robust technological solutions, stringent security policies, and a well-trained workforce. By implementing the strategies and best practices discussed, organizations can significantly reduce their vulnerability to cyber threats and ensure the confidentiality, integrity, and availability of their data. Continuous vigilance, regular security assessments, and adaptation to the ever-evolving threat landscape are paramount to maintaining a secure and productive remote workforce.
FAQ
What is a VPN, and why is it crucial for remote workers?
A Virtual Private Network (VPN) creates a secure, encrypted connection between a user’s device and a network, protecting data transmitted over public Wi-Fi or unsecured networks. It’s crucial for remote workers as it masks their IP address and encrypts their data, safeguarding against eavesdropping and unauthorized access.
How can I effectively train my remote employees on cybersecurity best practices?
Implement regular, engaging training sessions covering phishing awareness, strong password creation, safe browsing habits, and recognizing social engineering attempts. Use simulations and real-world examples to reinforce learning. Regular quizzes and updates ensure ongoing awareness.
What are the key differences between ZTNA and VPN?
While both enhance remote access security, Zero Trust Network Access (ZTNA) is more granular, verifying user and device access before granting network access, unlike VPNs which create a broad tunnel. ZTNA is generally considered more secure for accessing specific applications rather than entire networks.