In today’s fast-paced digital landscape, the need for robust security measures is more critical than ever. Advanced Threat Protection Solutions offer a comprehensive defense against evolving cyber threats, ensuring the safety of your valuable digital assets. Let’s delve into the world of advanced security and explore how these solutions can fortify your organization’s defenses.
Introduction to Advanced Threat Protection Solutions
Advanced Threat Protection Solutions refer to comprehensive security measures designed to safeguard organizations from sophisticated cyber threats that traditional security tools may not be able to detect or prevent.
These solutions utilize advanced technologies such as machine learning, artificial intelligence, and behavioral analytics to proactively identify and mitigate various cyber threats.
Common Threats Addressed by Advanced Threat Protection Solutions
- Malware: Advanced Threat Protection Solutions can detect and block various types of malware, including viruses, ransomware, and trojans.
- Phishing Attacks: These solutions can identify and prevent phishing emails and websites that attempt to steal sensitive information.
- Zero-Day Exploits: Advanced Threat Protection Solutions can detect and mitigate attacks exploiting vulnerabilities that are not yet known to the vendor.
- Insider Threats: These solutions can monitor and detect suspicious behavior from within the organization that may indicate a potential insider threat.
Importance of Robust Protection in Today’s Digital Landscape
In today’s interconnected world, where cyber threats are constantly evolving and becoming more sophisticated, having robust protection is crucial to safeguarding sensitive data, maintaining business continuity, and protecting the reputation of the organization.
Advanced Threat Protection Solutions play a vital role in enhancing the overall security posture of an organization by providing real-time threat detection, incident response capabilities, and continuous monitoring to mitigate risks effectively.
Components of Advanced Threat Protection Solutions
Advanced Threat Protection Solutions are comprised of various key components that work together to enhance cybersecurity measures and protect against sophisticated threats.
Threat Intelligence
- Threat intelligence involves gathering and analyzing data to identify potential threats and vulnerabilities.
- It provides insights into the tactics, techniques, and procedures used by cyber attackers.
- By leveraging threat intelligence, organizations can proactively defend against known threats and stay one step ahead of cybercriminals.
Behavior Analytics
- Behavior analytics focus on monitoring and analyzing user and entity behavior to detect anomalies or suspicious activities.
- It helps in identifying insider threats, compromised accounts, and other malicious behavior that traditional security measures may miss.
- By using machine learning algorithms, behavior analytics can detect patterns indicative of a potential cyber attack and trigger alerts for further investigation.
Sandboxing
- Sandboxing is a technique that isolates potentially malicious files or programs in a controlled environment for analysis.
- It allows security teams to execute suspicious code without risking the organization’s network or systems.
- By running files in a sandbox, security professionals can observe their behavior and determine if they pose a threat before allowing them to enter the network.
Real-World Example
In a real-world scenario, threat intelligence may alert security teams to a new malware strain targeting a specific software vulnerability. Behavior analytics can then detect unusual activity on the network related to this malware, prompting further investigation. Sandboxing can be used to analyze the suspicious file and prevent it from causing harm to the organization’s infrastructure.
Implementation of Advanced Threat Protection Solutions
Implementing Advanced Threat Protection Solutions within an organization involves several key steps to ensure maximum effectiveness and security.
Best Practices for Configuration and Fine-Tuning
- Regularly update and patch all security solutions to ensure they are equipped to handle the latest threats.
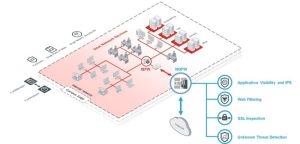
- Implement a layered approach to security by combining different solutions such as antivirus software, firewalls, and intrusion detection systems.
- Configure the solutions to provide real-time monitoring and alerts for any suspicious activity.
- Regularly review and analyze security logs to identify any potential threats and take proactive measures.
Challenges and Solutions
- Challenge: Integration with existing systems – Organizations may face compatibility issues when integrating new threat protection solutions with their current infrastructure.
- Challenge: False positives – Overly sensitive threat protection solutions may generate a high number of false positives, leading to alert fatigue and overlooking real threats.
- Challenge: Budget constraints – Implementing advanced threat protection solutions can be costly, especially for small to medium-sized businesses with limited resources.
Solution: Conduct thorough testing and ensure proper training for IT staff to seamlessly integrate the new solutions without disrupting existing operations.
Solution: Fine-tune the solutions to reduce false positives by adjusting sensitivity levels and creating custom rules based on the organization’s specific needs.
Solution: Prioritize critical assets and invest in essential security measures while exploring cost-effective solutions such as cloud-based security services.
Benefits of Advanced Threat Protection Solutions

Implementing Advanced Threat Protection Solutions offers various benefits for organizations looking to enhance their cybersecurity measures and protect against sophisticated threats. These benefits include:
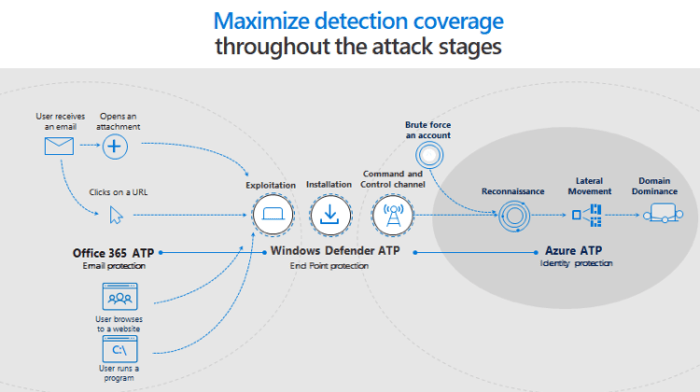
Enhanced Detection Capabilities
- Advanced Threat Protection Solutions utilize advanced technologies such as machine learning and artificial intelligence to detect and analyze threats in real-time.
- These solutions can identify and respond to emerging threats that traditional security measures might overlook.
Improved Incident Response Time
- By automating threat detection and response processes, organizations can significantly reduce the time it takes to identify and mitigate security incidents.
- Faster incident response helps minimize the impact of cyber attacks and prevents potential data breaches.
Comprehensive Security Coverage
- Advanced Threat Protection Solutions provide a holistic approach to cybersecurity by offering protection across multiple attack vectors, including email, web, and network.
- This comprehensive coverage ensures that organizations can defend against a wide range of threats effectively.
Cost-Efficiency
- While the initial investment in Advanced Threat Protection Solutions may seem significant, the long-term cost savings from preventing cyber attacks and data breaches outweigh the upfront expenses.
- Organizations can avoid costly remediation efforts and reputational damage by proactively implementing robust security measures.
Relationship between Advanced Threat Protection Solutions and Data Analytics
Data analytics plays a crucial role in enhancing the effectiveness of Advanced Threat Protection Solutions by providing deeper insights into security threats and patterns. By analyzing vast amounts of security data, organizations can better understand potential risks and vulnerabilities, allowing them to proactively strengthen their defenses.
Role of Machine Learning and AI in Analyzing Security Data
Machine learning and artificial intelligence are key components in the analysis of security data for threat detection. These technologies enable systems to learn from past incidents and adapt their detection capabilities to identify new and evolving threats in real-time. By continuously analyzing and refining security data, machine learning algorithms can effectively detect and respond to advanced cyber threats.
- Machine learning algorithms can identify patterns and anomalies in security data that may indicate a potential threat.
- AI-powered systems can automate the analysis of vast amounts of security data, enabling organizations to detect and respond to threats quickly.
- By leveraging machine learning and AI, Advanced Threat Protection Solutions can stay ahead of cybercriminals and mitigate risks effectively.
Predicting and Preventing Advanced Cyber Threats
Data analytics can help in predicting and preventing advanced cyber threats by utilizing historical data and trends to forecast potential risks. By analyzing security data in real-time and identifying patterns indicative of an upcoming attack, organizations can proactively implement security measures to prevent breaches.
Data analytics allows organizations to anticipate potential threats and take proactive steps to protect their systems and data.
- By analyzing user behavior and network traffic, data analytics can identify suspicious activities that may lead to a cyber attack.
- Predictive analytics can forecast emerging threats based on historical data, enabling organizations to strengthen their defenses preemptively.
- Data analytics can help organizations prioritize security measures and allocate resources effectively to mitigate the impact of advanced cyber threats.
As we conclude our exploration of Advanced Threat Protection Solutions, it becomes evident that investing in proactive security measures is paramount in safeguarding against sophisticated cyber threats. By embracing these cutting-edge solutions, organizations can bolster their cybersecurity posture and navigate the digital realm with confidence and resilience.
Popular Questions
What makes Advanced Threat Protection Solutions different from traditional security measures?
Advanced Threat Protection Solutions leverage advanced technologies like machine learning and behavior analytics to proactively detect and mitigate cyber threats, offering a more dynamic and effective defense compared to traditional security methods.
How can organizations overcome challenges during the implementation of these solutions?
Organizations can overcome implementation challenges by conducting thorough training for staff, regularly updating security protocols, and collaborating with experts to fine-tune the solutions according to their specific needs.
What role does data analytics play in enhancing Advanced Threat Protection Solutions?
Data analytics empowers these solutions by enabling organizations to analyze vast amounts of security data, identify patterns, and predict potential threats, thereby enhancing overall threat detection capabilities and proactive security measures.