Zero Trust Security Solutions sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset. In a world where digital threats loom large, the concept of Zero Trust Security emerges as a beacon of hope, promising a new era of impenetrable defense strategies.
As we delve deeper into the realm of cybersecurity, exploring the intricacies of Zero Trust Security Solutions unveils a tapestry of innovative practices and cutting-edge technologies that redefine the paradigm of protection in the digital age.
Zero Trust Security Solutions

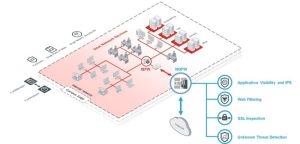
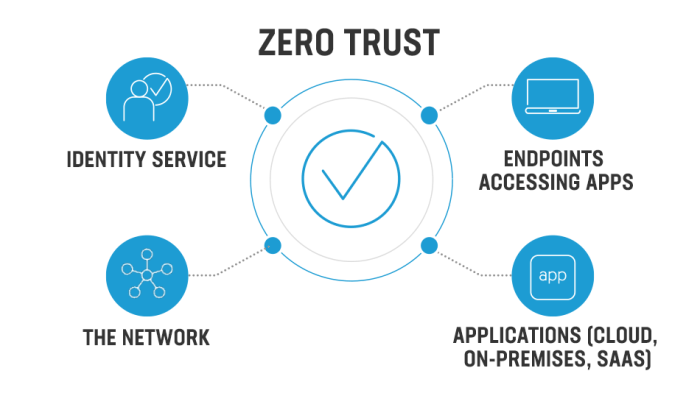
Zero Trust Security is a cybersecurity model based on the principle of “never trust, always verify.” This approach assumes that threats could be both external and internal, and thus, no entity should be automatically trusted. Instead, continuous verification is required for every access request, regardless of whether it originates from inside or outside the network.Implementing Zero Trust Security is crucial in modern cybersecurity practices due to the evolving threat landscape.
Traditional security measures like perimeter defenses are no longer sufficient to protect against sophisticated cyberattacks. By adopting Zero Trust principles, organizations can enhance their security posture and mitigate the risk of data breaches and unauthorized access.
Key Components of Zero Trust Security Solutions
- Micro-Segmentation: Dividing the network into smaller segments to limit lateral movement of threats.
- Multi-Factor Authentication (MFA): Requiring multiple forms of verification for user access.
- Continuous Monitoring: Real-time monitoring of network traffic and user activities for anomalies.
- Least Privilege Access: Granting users the minimum level of access required to perform their tasks.
- Zero Trust Architecture: Designing the network with Zero Trust principles from the ground up.
Companies Successfully Implementing Zero Trust Security Solutions
- Google: Implemented BeyondCorp, a Zero Trust security model that allows employees to work securely from any location without a traditional VPN.
- Microsoft: Utilizes Zero Trust principles in its security strategy, focusing on identity and access management to protect against cyber threats.
- Cisco: Embraced Zero Trust Security to enhance its network security posture and protect against advanced threats targeting its infrastructure.
Implementing Zero Trust Security Solutions
Implementing Zero Trust Security Solutions in an organization is a crucial step towards enhancing cybersecurity and protecting sensitive data. Below is a detailed step-by-step process to successfully implement Zero Trust Security Solutions:
Step-by-Step Process:
- Conduct a thorough assessment of the organization’s current security posture and identify potential vulnerabilities.
- Define the organization’s sensitive data and classify it based on importance and risk level.
- Implement strong authentication measures such as multi-factor authentication (MFA) for all users accessing the network.
- Segment the network to create zones of access based on user roles and data sensitivity.
- Monitor and log all network traffic to detect any unusual behavior or potential threats.
- Regularly update and patch all systems and software to ensure they are protected against known vulnerabilities.
- Train employees on cybersecurity best practices and the importance of adhering to Zero Trust principles.
Preventing Data Breaches and Unauthorized Access:
- Zero Trust Security Solutions help prevent data breaches by assuming that threats exist both inside and outside the network perimeter.
- By enforcing strict access controls and continuously verifying user identity, Zero Trust Security Solutions limit the risk of unauthorized access to sensitive data.
- Implementing encryption protocols further enhances security by protecting data both in transit and at rest.
- Regularly auditing and monitoring user activity helps in detecting any suspicious behavior and mitigating potential threats before they escalate.
Challenges Organizations May Face:
- Resistance to change from employees accustomed to traditional security models.
- Complexity in integrating Zero Trust Security Solutions with existing infrastructure and applications.
- Ensuring seamless user experience while implementing additional security measures.
- Budget constraints and resource limitations for implementing and maintaining Zero Trust Security Solutions.
Best Practices for Adopting Zero Trust Security Solutions:
- Start with a pilot project to test the effectiveness of Zero Trust Security Solutions in a controlled environment.
- Collaborate with all stakeholders, including IT teams, security professionals, and business leaders, to ensure alignment with organizational goals.
- Regularly review and update security policies and procedures to adapt to evolving threats and technology changes.
- Invest in employee training and awareness programs to promote a culture of cybersecurity within the organization.
Benefits of Zero Trust Security Solutions
Zero Trust Security Solutions offer a range of advantages over traditional security measures, enhancing overall cybersecurity posture and data protection.
Enhanced Security Posture
- Zero Trust Security Solutions reduce the risk of unauthorized access by requiring verification for every user and device trying to connect to the network.
- By implementing strict access controls and continuous monitoring, organizations can detect and respond to potential threats more effectively.
- Zero Trust model assumes that threats are already inside the network, thereby providing a more proactive approach to security.
Improved Data Protection and Privacy
- Zero Trust Security Solutions help organizations protect sensitive data by segmenting their networks and enforcing least privilege access.
- By encrypting data both at rest and in transit, Zero Trust model ensures that data remains secure even if a breach occurs.
- Organizations can also achieve compliance with data privacy regulations more easily by implementing Zero Trust Security Solutions.
Real-world Examples
- Google implemented Zero Trust Security model known as BeyondCorp, which helped them improve security and reduce the risk of data breaches.
- Pfizer, a pharmaceutical company, adopted Zero Trust Security Solutions to protect their valuable intellectual property and sensitive research data.
- The US Department of Defense has also embraced Zero Trust principles to enhance the security of their vast network infrastructure.
Zero Trust Security Solutions vs. Traditional Security Measures
When comparing Zero Trust Security Solutions with traditional perimeter-based security approaches, it is crucial to understand the fundamental differences in their methodologies and effectiveness in today’s cyber threat landscape.
Limitations of Traditional Security Measures
Traditional security measures rely heavily on perimeter defenses that assume once inside the network, all users and devices are trustworthy. This approach creates vulnerabilities as cyber threats become more sophisticated, bypassing traditional security controls.
- Perimeter security can be breached, allowing attackers to move laterally within the network undetected.
- Legacy security tools often lack visibility into user and device behaviors, making it challenging to detect insider threats or anomalous activities.
- Static trust models based on IP addresses or user credentials are no longer effective in a dynamic and cloud-based IT environment.
Adaptation to the Evolving Cybersecurity Landscape
Zero Trust Security Solutions address the limitations of traditional security measures by adopting a holistic approach that verifies and validates every user and device attempting to access the network, regardless of their location.
- Zero Trust implements strict access controls and micro-segmentation to limit lateral movement and contain potential security breaches.
- Continuous monitoring of user behaviors and device activities enables early detection of anomalies and potential threats.
- Zero Trust frameworks focus on dynamic trust assessment based on real-time context, such as user behavior, device health, and network conditions.
Organizational Shift Towards Zero Trust Security Solutions
Organizations are increasingly moving towards Zero Trust Security Solutions to enhance their cybersecurity posture and better protect their sensitive data and critical assets.
- The rise of remote work and cloud adoption has expanded the attack surface, necessitating a more secure and adaptive security approach like Zero Trust.
- Regulatory requirements and compliance standards are pushing organizations to implement more robust security measures, making Zero Trust a preferred choice for mitigating risks.
- The growing sophistication of cyber threats, including ransomware and insider attacks, requires a proactive and dynamic security model like Zero Trust to stay ahead of evolving threats.
Data Analytics in Cybersecurity
Data analytics plays a crucial role in strengthening cybersecurity measures by analyzing vast amounts of data to identify patterns, anomalies, and potential threats. By leveraging data analytics tools and techniques, organizations can enhance their ability to detect and mitigate cyber threats effectively.
Detection and Mitigation of Cyber Threats
- Data analytics tools can monitor network traffic and user behavior in real-time to identify suspicious activities or deviations from normal patterns.
- By analyzing historical data and correlating information from multiple sources, data analytics can help in early detection of cyber threats.
- Machine learning algorithms can be utilized to predict potential security breaches and proactively respond to emerging threats.
Proactive Cybersecurity Strategies
- Organizations can use data analytics to assess their security posture, identify vulnerabilities, and prioritize security measures to prevent future cyber attacks.
- By analyzing data from various sources, including security logs, threat intelligence feeds, and endpoint devices, organizations can continuously improve their cybersecurity defenses.
Cybersecurity Incident Response
- Data analytics enables organizations to investigate security incidents more efficiently by analyzing data logs, network traffic, and user activity to determine the scope and impact of an attack.
- By using data analytics, organizations can quickly contain and remediate security incidents, minimizing the damage and reducing the time to recovery.
In conclusion, Zero Trust Security Solutions stand as a formidable fortress against cyber threats, embodying a proactive approach that reshapes the landscape of defense strategies. With its emphasis on continuous verification and strict access controls, this security framework heralds a future where trust is earned, not assumed, in the realm of digital protection.
General Inquiries
What is Zero Trust Security?
Zero Trust Security is a cybersecurity model that eliminates the concept of trust within a network, requiring verification from anyone trying to access resources.
How do Zero Trust Security Solutions enhance data protection?
Zero Trust Security Solutions enhance data protection by ensuring that all access attempts are verified and authenticated, reducing the risk of unauthorized breaches.
Why are organizations moving towards Zero Trust Security Solutions?
Organizations are adopting Zero Trust Security Solutions due to the increasing sophistication of cyber threats and the need for a more robust defense mechanism beyond traditional security measures.