In today’s interconnected world, cybersecurity threats loom larger than ever. Businesses, regardless of size, face a constant barrage of sophisticated attacks aiming to steal data, disrupt operations, and inflict financial damage. This necessitates a robust and proactive approach to security, and increasingly, organizations are turning to Managed Cybersecurity Solutions (MCS) to bolster their defenses. MCS offer a compelling alternative to maintaining an expensive in-house team, providing comprehensive protection tailored to specific needs and budgets.
This guide delves into the multifaceted world of managed cybersecurity, exploring its core components, benefits, and the crucial factors to consider when selecting a provider. We will examine various solution types, address common security threats, and highlight the role of emerging technologies like AI and automation in shaping the future of cybersecurity management. Understanding the intricacies of MCS is no longer a luxury; it’s a necessity for survival in the digital age.
Choosing the Right Managed Cybersecurity Solution
Selecting the optimal managed cybersecurity solution requires careful consideration of your business’s specific needs, budget, and risk tolerance. A poorly chosen solution can leave your organization vulnerable, while an overly complex or expensive one might be unnecessary. This section provides guidance on navigating the selection process effectively.
Checklist for Evaluating Managed Security Providers
A thorough evaluation of potential managed security providers is crucial. This checklist helps streamline the process and ensure you’re making an informed decision. Consider these key aspects before committing to a provider.
- Security Expertise and Certifications: Verify the provider’s certifications (e.g., ISO 27001, SOC 2) and experience in handling similar-sized businesses or industries.
- Service Offerings: Assess whether their services align with your specific security needs (e.g., threat detection, incident response, vulnerability management, endpoint protection). Do they offer 24/7 monitoring and support?
- Technology Stack: Understand the technologies they utilize and ensure compatibility with your existing infrastructure. Are they using leading-edge tools and technologies?
- Customer References and Reviews: Request references and independently verify customer satisfaction through online reviews or industry reports. What are other clients saying about their experience?
- Incident Response Plan: Review their detailed incident response plan to ensure it’s comprehensive and aligns with your business continuity strategy. How quickly can they respond to a security breach?
- Compliance and Regulations: Confirm their adherence to relevant industry regulations and compliance standards (e.g., GDPR, HIPAA). Do they understand and can they meet your regulatory requirements?
- Scalability and Flexibility: Assess the provider’s ability to scale their services to meet your evolving needs as your business grows or changes.
The Importance of Service Level Agreements (SLAs)
Service Level Agreements (SLAs) are legally binding contracts that define the specific services a managed security provider will deliver, including performance metrics, response times, and uptime guarantees. A well-defined SLA is essential for ensuring accountability and mitigating risks. Without a clear SLA, you risk ambiguity regarding responsibilities and service quality. For example, a poorly defined SLA might not specify response times for security incidents, leaving your business vulnerable to prolonged downtime and data breaches.
A strong SLA will detail metrics such as mean time to resolution (MTTR) for security incidents, guaranteed uptime for security monitoring systems, and escalation procedures for critical issues.
Pricing Models of Managed Cybersecurity Solutions
Managed cybersecurity solutions typically employ various pricing models, each with its advantages and disadvantages. Understanding these models is vital for budget planning and cost optimization.
- Per-Device Pricing: This model charges a fee for each device protected, making it suitable for businesses with a clearly defined number of endpoints.
- Per-User Pricing: This model charges a fee per user, which is advantageous for businesses focusing on user-level security and access management.
- Tiered Pricing: This offers different service packages at varying price points, allowing businesses to select a level of protection that matches their budget and needs. For example, a basic package might offer threat detection only, while a premium package could include incident response and vulnerability management.
- Usage-Based Pricing: This model charges based on actual usage, offering flexibility but requiring careful monitoring of consumption to avoid unexpected costs.
Decision Tree for Selecting a Managed Cybersecurity Solution
The selection process can be simplified using a decision tree. This example illustrates a basic decision-making process, which should be tailored to your organization’s specific context.
Start: What is your budget?
Branch 1 (Low Budget): Consider a basic, cloud-based solution with essential threat detection and prevention capabilities. Focus on providers offering tiered pricing options.
Branch 2 (Medium Budget): Explore solutions with more advanced features like incident response, vulnerability management, and 24/7 monitoring. Thoroughly review SLAs and service offerings.
Branch 3 (High Budget): Invest in a comprehensive solution with advanced threat intelligence, proactive security measures, and dedicated security experts. Prioritize providers with strong security certifications and a proven track record.
Final Step: Once a potential solution is identified, conduct a thorough evaluation using the checklist provided earlier.
Cybersecurity Solutions (Broader Context)

The cybersecurity landscape is a constantly evolving battlefield, characterized by increasingly sophisticated threats and a growing reliance on interconnected digital systems. Understanding this landscape is crucial for organizations of all sizes, from small businesses to multinational corporations, to effectively protect their valuable data and assets. This section provides an overview of the current state of cybersecurity, highlighting the evolution of threats and emerging vulnerabilities.The past decade has witnessed a dramatic shift in the nature and scale of cybersecurity threats.
Early threats primarily focused on individual vulnerabilities and simple attacks. Today, we see a surge in highly organized, state-sponsored attacks, sophisticated ransomware campaigns, and the exploitation of supply chain vulnerabilities. The rise of cloud computing, the Internet of Things (IoT), and remote work has significantly expanded the attack surface, making organizations more vulnerable than ever before. For example, the SolarWinds attack in 2020 demonstrated the devastating impact of a compromised software supply chain, affecting thousands of organizations worldwide.
Emerging Cybersecurity Threats and Vulnerabilities
Several emerging threats are pushing the boundaries of traditional cybersecurity defenses. Artificial intelligence (AI) is being increasingly used by both attackers and defenders, leading to an arms race in cybersecurity capabilities. AI-powered attacks can automate malicious activities, making them more efficient and difficult to detect. Simultaneously, AI is also being used to enhance security defenses, such as threat detection and incident response.
Another significant threat is the increasing sophistication of ransomware attacks, with attackers demanding larger ransoms and employing more destructive tactics. The rise of IoT devices, while offering convenience, introduces a vast number of potential entry points for attackers, many of which lack adequate security measures. Finally, the growing reliance on cloud services introduces new vulnerabilities, particularly around data breaches and misconfigurations.
For instance, the increasing use of cloud storage solutions requires robust access controls and encryption to prevent unauthorized access.
The Importance of a Layered Security Approach
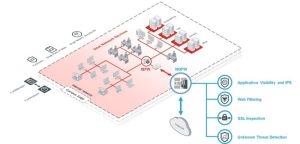
A layered security approach is paramount in today’s complex threat landscape. This strategy involves implementing multiple layers of security controls to protect against a wide range of threats. No single security solution can provide complete protection; a layered approach mitigates the risk of a single point of failure. These layers can include network security (firewalls, intrusion detection systems), endpoint security (antivirus, endpoint detection and response), data security (encryption, access controls), and identity and access management (IAM).
A robust security information and event management (SIEM) system is also crucial for monitoring and analyzing security events across the organization. The layered approach ensures that even if one layer is compromised, other layers can still provide protection. For example, even if a firewall is bypassed, intrusion detection systems can detect malicious activity, and endpoint security can prevent malware execution.
This multi-faceted approach significantly enhances an organization’s overall security posture.
Future Trends in Managed Cybersecurity
The landscape of cybersecurity is constantly evolving, driven by technological advancements and the ever-increasing sophistication of cyber threats. Understanding and adapting to these future trends is crucial for organizations seeking to maintain robust and effective managed security solutions. This section will explore several key areas shaping the future of managed cybersecurity.
Artificial Intelligence and Machine Learning in Managed Security
AI and ML are rapidly transforming managed security services. These technologies enhance threat detection and response capabilities by analyzing vast amounts of security data in real-time, identifying patterns and anomalies that might otherwise go unnoticed. For example, AI-powered systems can analyze network traffic to detect suspicious activity, such as malware infections or unauthorized access attempts, far more quickly and efficiently than human analysts alone.
Machine learning algorithms continuously learn and adapt, improving their accuracy over time and reducing the number of false positives. This leads to faster response times, reduced operational costs, and a more proactive approach to threat management. Furthermore, AI can automate repetitive tasks, freeing up human analysts to focus on more complex and strategic security challenges.
Automation in Managed Security Services
Automation is playing an increasingly vital role in improving the efficiency and effectiveness of managed security services. Automating tasks such as vulnerability scanning, patch management, and incident response significantly reduces the workload on security teams, allowing them to focus on higher-level tasks such as threat intelligence analysis and security strategy development. Automation also minimizes human error, a significant factor in many security breaches.
For instance, automated systems can rapidly deploy security patches across an organization’s infrastructure, minimizing the window of vulnerability to exploitation. The use of Robotic Process Automation (RPA) can streamline routine tasks like user account provisioning and de-provisioning, improving efficiency and reducing the risk of human error.
Cloud-Based Managed Security Solutions
The increasing adoption of cloud computing presents both challenges and opportunities for managed cybersecurity. Cloud-based solutions offer scalability, flexibility, and cost-effectiveness, making them attractive to organizations of all sizes. However, securing cloud environments requires specialized expertise and a different approach to traditional on-premise security. Challenges include ensuring data privacy and compliance with regulations such as GDPR, managing access control across multiple cloud providers, and protecting against cloud-specific threats like account hijacking and data breaches.
Opportunities include leveraging cloud-native security tools and services, such as cloud access security brokers (CASBs) and security information and event management (SIEM) platforms, to enhance security posture and gain better visibility into cloud activity. The ability to scale security resources up or down based on demand is a key advantage.
Impact of Remote Work on Managed Cybersecurity Strategies
The widespread adoption of remote work has significantly broadened the attack surface for organizations. With employees accessing company resources from various locations and devices, managing security becomes significantly more complex. Managed cybersecurity strategies must adapt to address this shift, focusing on securing remote access points, implementing robust endpoint protection, and providing security awareness training to remote workers. Multi-factor authentication (MFA) becomes crucial to prevent unauthorized access.
Regular security assessments and vulnerability scans are essential to identify and address potential weaknesses in remote work setups. Furthermore, robust incident response plans are necessary to quickly contain and mitigate security breaches that may occur within the distributed workforce environment. For example, companies are increasingly adopting Zero Trust Network Access (ZTNA) solutions to secure access to internal resources regardless of location.
Ultimately, the decision to implement Managed Cybersecurity Solutions represents a strategic investment in the long-term health and prosperity of any organization. By carefully evaluating needs, selecting a reputable provider, and maintaining proactive engagement, businesses can significantly reduce their vulnerability to cyber threats. The future of cybersecurity is undeniably intertwined with managed services, offering a scalable, adaptable, and cost-effective pathway to robust protection in an ever-evolving threat landscape.
Proactive security is not merely a best practice; it’s a business imperative.
FAQ Resource
What is the difference between managed and unmanaged security services?
Unmanaged services provide the tools and technologies but require your internal team to manage and monitor them. Managed services handle the entire process, from monitoring and threat detection to incident response.
How much does a managed cybersecurity solution typically cost?
Pricing varies greatly depending on the size of your organization, the specific services required, and the provider. Expect a range of options, from subscription-based models to more customized packages.
What is the role of Service Level Agreements (SLAs) in managed security?
SLAs define the specific performance expectations and responsibilities of the managed security provider, ensuring a certain level of service and accountability.
How can I ensure my data remains compliant with regulations like GDPR or CCPA when using a managed security provider?
Choose a provider with a strong track record of compliance and data protection, and carefully review their data handling practices and security certifications.