The healthcare industry faces a unique and evolving cybersecurity threat landscape. Protecting sensitive patient data, complying with stringent regulations like HIPAA and GDPR, and safeguarding critical medical infrastructure require sophisticated and multifaceted solutions. This exploration delves into the crucial aspects of cybersecurity in healthcare, examining the challenges, solutions, and future trends shaping this vital sector.
From network security and endpoint protection to data encryption and incident response, we will analyze the diverse strategies employed to mitigate risks and ensure the confidentiality, integrity, and availability of healthcare information. We’ll also consider the human element, emphasizing the importance of employee training and awareness in building a robust cybersecurity posture.
Introduction to Healthcare Cybersecurity
The healthcare industry faces a unique and increasingly complex cybersecurity landscape. The convergence of sensitive patient data, interconnected medical devices, and a growing reliance on digital technologies creates a fertile ground for cyberattacks with potentially devastating consequences. Protecting patient information and ensuring the continued operation of critical healthcare systems requires a robust and proactive cybersecurity strategy.The sheer volume and sensitivity of data handled by healthcare organizations present significant challenges.
This data is often highly valuable to cybercriminals, who can exploit breaches for financial gain, identity theft, or even to disrupt critical services. Effective cybersecurity measures are paramount to mitigate these risks.
Sensitive Data and Associated Risks in Healthcare
Healthcare organizations manage a wide array of sensitive data, including Protected Health Information (PHI) as defined by HIPAA, genetic information, medical images, patient financial data, and intellectual property related to research and development. Breaches involving this data can lead to significant financial penalties, reputational damage, loss of patient trust, and legal ramifications. For example, a breach exposing patient financial information could lead to identity theft and fraudulent charges, while the exposure of genetic information could have significant implications for an individual’s health insurance and employment prospects.
The unauthorized access or disclosure of medical images could violate patient privacy and potentially lead to misdiagnosis or inappropriate treatment.
Relevant Regulations and Compliance Standards
Several regulations and compliance standards govern the handling of sensitive data in healthcare. The Health Insurance Portability and Accountability Act (HIPAA) in the United States mandates the protection of PHI. The General Data Protection Regulation (GDPR) in Europe provides a comprehensive framework for data protection and privacy rights. Other regional and national regulations exist, all emphasizing the need for robust security measures to protect patient data and maintain compliance.
Non-compliance can result in substantial fines, legal action, and reputational harm. These regulations necessitate a multifaceted approach to cybersecurity, encompassing technical safeguards, administrative processes, and employee training. For example, HIPAA requires organizations to implement administrative safeguards such as policies and procedures for handling PHI, physical safeguards such as secure facilities and access controls, and technical safeguards such as encryption and access controls.
GDPR similarly requires organizations to implement appropriate technical and organizational measures to ensure the security and confidentiality of personal data.
Types of Cybersecurity Solutions for Healthcare
Protecting sensitive patient data and ensuring the reliable operation of healthcare systems requires a multi-layered approach to cybersecurity. This necessitates the implementation of a range of solutions designed to address specific vulnerabilities and threats. The following sections detail key categories of cybersecurity solutions commonly employed in healthcare settings.
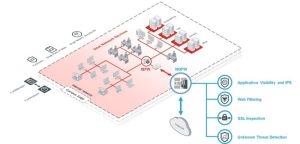
Network Security Solutions
Network security focuses on protecting the healthcare organization’s network infrastructure from unauthorized access and malicious activity. This involves implementing firewalls, intrusion detection/prevention systems (IDS/IPS), and virtual private networks (VPNs) to control network traffic and prevent threats from entering the network. Robust network segmentation further isolates sensitive data and critical systems, limiting the impact of a successful breach. Regular network vulnerability scans and penetration testing identify and address weaknesses before they can be exploited.
Endpoint Security Solutions
Endpoint security protects individual devices, such as computers, laptops, tablets, and smartphones, that connect to the healthcare network. This includes installing and maintaining antivirus software, endpoint detection and response (EDR) solutions, and data loss prevention (DLP) tools. Regular software updates and patching are crucial to address known vulnerabilities. Strong access control measures, including multi-factor authentication (MFA), are essential to prevent unauthorized access to sensitive data stored on these devices.
Data Loss Prevention (DLP) Solutions
Data loss prevention (DLP) solutions are designed to prevent sensitive patient data from leaving the healthcare organization’s control. These solutions monitor data movement across the network and identify attempts to exfiltrate protected health information (PHI). DLP tools can block unauthorized data transfers, encrypt sensitive data at rest and in transit, and provide alerts when suspicious activity is detected.
Implementing robust DLP measures is crucial for compliance with regulations like HIPAA.
Security Information and Event Management (SIEM) Solutions
Security information and event management (SIEM) solutions collect and analyze security logs from various sources across the healthcare network. This provides a centralized view of security events, allowing security teams to identify and respond to threats more effectively. SIEM systems can detect anomalies, generate alerts on suspicious activity, and provide valuable insights into security posture. Effective SIEM implementation requires careful configuration and ongoing monitoring to ensure its effectiveness.
| Solution Type | Description | Benefits | Examples |
|---|---|---|---|
| Network Security | Protects the network infrastructure from unauthorized access and malicious activity. | Enhanced network security, reduced risk of breaches, improved compliance. | Firewalls, Intrusion Detection/Prevention Systems (IDS/IPS), VPNs, Network Segmentation |
| Endpoint Security | Protects individual devices connected to the network. | Protection against malware, data breaches, and unauthorized access. | Antivirus software, Endpoint Detection and Response (EDR), Data Loss Prevention (DLP) tools, Multi-factor authentication (MFA) |
| Data Loss Prevention (DLP) | Prevents sensitive data from leaving the organization’s control. | Reduced risk of data breaches, improved compliance, enhanced data security. | Data encryption, access control, data masking, anomaly detection |
| Security Information and Event Management (SIEM) | Collects and analyzes security logs to detect and respond to threats. | Improved threat detection, faster incident response, enhanced security visibility. | Splunk, IBM QRadar, LogRhythm |
Securing Medical Devices and IoT Infrastructure
Securing medical devices and Internet of Things (IoT) infrastructure presents unique challenges due to their diverse operating systems, limited processing power, and often outdated security features. A layered approach is necessary, combining network segmentation to isolate these devices from the rest of the network, robust access control measures to limit who can interact with them, and regular security patching and updates to address vulnerabilities.
Furthermore, employing dedicated security solutions designed specifically for medical devices and IoT devices is crucial. This might involve specialized firewalls, intrusion detection systems, and security gateways designed to handle the unique communication protocols and security requirements of these devices. The use of micro-segmentation can further isolate sensitive devices and limit the impact of a breach. Regular security assessments and vulnerability scans are critical to maintain a strong security posture for this often-overlooked area of the healthcare IT infrastructure.
Data Security and Privacy in Healthcare

Protecting patient data is paramount in healthcare. The sensitive nature of medical information necessitates robust security measures to ensure confidentiality, integrity, and availability (CIA triad). Failure to do so can result in significant legal repercussions, reputational damage, and erosion of patient trust. This section details key strategies for securing healthcare data.
Encrypting Sensitive Patient Data
Data encryption is a fundamental aspect of protecting patient data, both at rest (when stored) and in transit (while being transmitted). Encryption transforms readable data (plaintext) into an unreadable format (ciphertext) using a cryptographic key. Only those with the correct key can decrypt the data and access its original form. For data at rest, strong encryption algorithms like AES-256 should be employed for all stored patient data, including electronic health records (EHRs), medical images, and billing information.
Database encryption, full disk encryption (FDE), and file-level encryption are common methods. For data in transit, HTTPS (with TLS/SSL) is essential for securing communication between systems and users. Virtual Private Networks (VPNs) can further enhance security by creating encrypted tunnels for data transmission over public networks. Regular key management practices, including key rotation and secure key storage, are crucial to maintain the effectiveness of encryption.
Access Control and Identity Management
Effective access control and identity management are crucial for limiting who can access patient data and what actions they can perform. This involves implementing a robust role-based access control (RBAC) system, where users are assigned specific roles with defined permissions based on their job responsibilities. For example, a nurse might have access to view patient records but not modify them, while a physician might have broader access privileges.
Strong authentication mechanisms, such as multi-factor authentication (MFA), should be implemented to verify user identities before granting access. Regular security audits and access reviews should be conducted to ensure that permissions remain appropriate and that no unauthorized access has occurred. The principle of least privilege should always be followed, granting users only the minimum necessary access rights to perform their duties.
This minimizes the potential damage from a security breach.
Secure Data Backup and Recovery Plan for a Hypothetical Hospital System
A comprehensive data backup and recovery plan is critical for business continuity and data protection. Consider a hypothetical hospital system, “City General Hospital,” with multiple departments and locations. City General Hospital needs a robust plan encompassing the following:
Backup Strategy: A 3-2-1 backup strategy is recommended. This involves maintaining three copies of data, on two different media types, with one copy stored offsite. For example, daily incremental backups to local disk, weekly full backups to tape, and monthly offsite cloud backups.
Backup Schedule: Daily incremental backups for operational data, weekly full backups for critical data, and monthly full backups for archiving. The offsite backup should be conducted monthly, with regular testing of the recovery process.
Recovery Procedures: Detailed, documented procedures for restoring data from backups in case of disaster or data loss. This includes specifying recovery time objectives (RTOs) and recovery point objectives (RPOs) for different systems. Regular testing of the recovery process is essential to ensure its effectiveness.
Timeline: RTOs and RPOs should be defined for different systems based on their criticality. For example, the EHR system might have an RTO of 4 hours and an RPO of 24 hours, while less critical systems might have longer recovery times. The plan should Artikel specific actions and responsibilities for each member of the recovery team, ensuring a coordinated response in case of an incident.
Security Considerations: Backups should be encrypted both at rest and in transit to protect against unauthorized access. Access to backup systems should be strictly controlled, with appropriate authentication and authorization mechanisms in place. Regular security audits and vulnerability assessments should be conducted to identify and mitigate potential security risks.
Securing healthcare data and systems is not merely a technological challenge; it’s a fundamental responsibility. By implementing comprehensive cybersecurity solutions, fostering a culture of security awareness, and adapting to the ever-changing threat landscape, healthcare organizations can effectively protect patient information, maintain operational integrity, and build trust with their communities. The future of healthcare cybersecurity lies in proactive risk management, innovative technologies, and collaborative partnerships.
Question & Answer Hub
What is the biggest cybersecurity threat to healthcare organizations?
Ransomware attacks are currently a major threat, as they can disrupt operations and potentially compromise sensitive patient data. Phishing attacks targeting employees remain a significant entry point for malicious actors.
How can healthcare organizations improve employee cybersecurity awareness?
Regular security awareness training, phishing simulations, and clear communication protocols are essential. Training should be engaging, relevant, and tailored to the specific roles and responsibilities of employees.
What is the role of AI in healthcare cybersecurity?
AI and machine learning can enhance threat detection, incident response, and vulnerability management. They can analyze vast amounts of data to identify patterns and anomalies, enabling faster and more effective responses to security incidents.
How can a small clinic implement basic cybersecurity measures?
Start with strong passwords, multi-factor authentication, regular software updates, employee training, and robust data backup procedures. Consider cloud-based solutions for data storage and security.