Cybersecurity Risk Management Solutions sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail with casual formal language style and brimming with originality from the outset.
In today’s interconnected world, the need for robust cybersecurity risk management solutions has never been more critical. From defending against sophisticated cyber threats to safeguarding sensitive data, these solutions play a pivotal role in ensuring the security and integrity of organizations’ digital assets. Let’s delve into the intricacies of Cybersecurity Risk Management Solutions and explore how they are reshaping the landscape of cybersecurity practices.
Introduction to Cybersecurity Risk Management Solutions

In today’s digital landscape, cybersecurity risk management plays a crucial role in safeguarding organizations’ sensitive data and systems from cyber threats. With the increasing reliance on digital technologies, the importance of implementing effective cybersecurity measures cannot be overstated.
Common Cyber Threats
- Malware: malicious software designed to disrupt, damage, or gain unauthorized access to computer systems.
- Phishing: fraudulent attempts to obtain sensitive information by disguising as a trustworthy entity.
- Ransomware: a type of malware that encrypts files and demands payment for their release.
- DDoS Attacks: Distributed Denial of Service attacks that overload systems, causing them to crash.
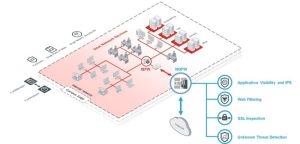
Role of Cybersecurity Risk Management Solutions
Cybersecurity risk management solutions are essential for identifying, assessing, and mitigating potential risks to an organization’s data and systems. These solutions encompass a range of tools, practices, and policies aimed at enhancing the overall security posture of an organization.
Key Components of Cybersecurity Risk Management Solutions

Cybersecurity risk management solutions are essential for protecting organizations from cyber threats and ensuring the security of their data and systems. A robust cybersecurity risk management framework consists of key components that work together to identify, assess, and mitigate risks effectively.
Threat Intelligence and Vulnerability Management
Threat intelligence involves gathering information about potential threats and vulnerabilities that could affect an organization’s cybersecurity. This includes monitoring for emerging threats, analyzing trends, and staying informed about the latest cybersecurity risks. Vulnerability management, on the other hand, focuses on identifying and addressing weaknesses in systems and applications that could be exploited by cyber attackers. By combining threat intelligence with vulnerability management, organizations can proactively protect against potential threats and reduce their risk exposure.
- Threat intelligence involves monitoring for potential threats and analyzing trends to stay ahead of cyber attackers.
- Vulnerability management focuses on identifying and addressing weaknesses in systems and applications to prevent exploitation by attackers.
- By integrating threat intelligence and vulnerability management, organizations can strengthen their cybersecurity posture.
Risk Assessment and Mitigation Strategies
Risk assessment is a crucial component of cybersecurity risk management solutions, as it helps organizations identify and prioritize risks based on their potential impact and likelihood of occurrence. By conducting regular risk assessments, organizations can gain a better understanding of their risk landscape and make informed decisions about where to focus their resources for mitigation.
- Risk assessment helps organizations identify and prioritize risks based on impact and likelihood of occurrence.
- By conducting regular risk assessments, organizations can proactively manage and mitigate potential cybersecurity risks.
- Implementing mitigation strategies based on risk assessment findings strengthens the organization’s overall security posture.
Implementation of Cybersecurity Risk Management Solutions
Implementing cybersecurity risk management solutions is a crucial step for organizations to protect their sensitive data and systems from potential cyber threats. It involves a systematic approach to selecting, integrating, and managing these solutions effectively.
Selecting and Implementing Solutions
When selecting cybersecurity risk management solutions, organizations need to consider factors such as the specific security needs, budget constraints, and compatibility with existing IT infrastructure. Once the solutions are chosen, the implementation process typically involves the following steps:
- Evaluating the current cybersecurity posture to identify vulnerabilities and areas of improvement.
- Developing a detailed implementation plan outlining the deployment of security tools and technologies.
- Testing the solutions in a controlled environment to ensure compatibility and effectiveness.
- Training employees on how to use the new security measures and protocols.
- Monitoring and evaluating the implemented solutions regularly to address any emerging threats or weaknesses.
Best Practices for Integration
Integrating cybersecurity risk management solutions into existing IT infrastructure requires careful planning and execution. Some best practices include:
- Ensuring seamless integration with current systems to minimize disruption to daily operations.
- Regularly updating and patching security software to address new vulnerabilities and threats.
- Implementing multi-factor authentication and encryption protocols to enhance data protection.
- Leveraging automation tools for real-time threat detection and response.
Challenges During Implementation
Organizations may face several challenges during the implementation phase of cybersecurity risk management solutions, such as:
- Resistance to change from employees who are accustomed to existing processes.
- Budget constraints that limit the scope of security measures that can be implemented.
- Complexity of integrating new solutions with legacy systems and applications.
- Lack of skilled cybersecurity professionals to manage and maintain the implemented solutions.
Cybersecurity Solutions Data Analytics
Data analytics plays a crucial role in enhancing cybersecurity solutions by providing valuable insights into potential security threats and vulnerabilities. By leveraging data analytics tools and techniques, organizations can effectively identify, monitor, and respond to cyber threats in real-time, enabling them to strengthen their overall security posture.
Role of Data Analytics in Enhancing Cybersecurity Solutions
- Data analytics helps in analyzing large volumes of data from various sources to detect patterns and anomalies that may indicate a security breach.
- By utilizing machine learning algorithms and artificial intelligence, data analytics can predict and prevent future cyber attacks based on historical data and patterns.
- It enables organizations to prioritize security alerts and incidents based on their severity and impact, allowing for more efficient incident response and mitigation strategies.
Identifying Potential Security Breaches with Data Analytics
- Data analytics can help in detecting unauthorized access attempts, unusual network traffic patterns, and suspicious behavior that may indicate a security breach.
- By correlating data from different sources such as logs, network traffic, and user behavior, organizations can uncover hidden threats and vulnerabilities that may go unnoticed with traditional security measures.
- Through advanced analytics, organizations can proactively identify and address security gaps before they are exploited by malicious actors, reducing the risk of data breaches and cyber attacks.
Importance of Real-Time Data Analysis for Proactive Threat Detection and Response
- Real-time data analysis allows organizations to monitor their systems and networks continuously, enabling them to detect and respond to security incidents as they occur.
- By analyzing data in real-time, organizations can identify emerging threats and trends, enabling them to take immediate action to prevent potential security breaches.
- Proactive threat detection through real-time data analysis helps organizations stay ahead of cyber criminals and minimize the impact of security incidents on their operations and reputation.
As we wrap up our exploration of Cybersecurity Risk Management Solutions, it becomes evident that proactive risk mitigation strategies and robust frameworks are essential components in safeguarding against evolving cyber threats. By implementing these solutions effectively and staying abreast of emerging technologies, organizations can fortify their defenses and navigate the complex cybersecurity landscape with confidence.
Commonly Asked Questions
What are the key components of a cybersecurity risk management framework?
A cybersecurity risk management framework comprises essential elements such as risk assessment, threat intelligence, vulnerability management, and mitigation strategies to effectively mitigate cyber threats.
How can organizations integrate cybersecurity risk management solutions into their existing IT infrastructure?
Organizations can integrate cybersecurity risk management solutions by following best practices, conducting thorough assessments of their IT environment, and ensuring seamless compatibility with existing systems.
What role does data analytics play in enhancing cybersecurity solutions?
Data analytics plays a crucial role in cybersecurity solutions by enabling organizations to analyze vast amounts of data in real-time, identify security breaches, and proactively detect and respond to potential threats.