The cloud’s transformative power has revolutionized how businesses operate, yet this shift introduces new security complexities. Understanding cloud security solutions is no longer optional; it’s paramount for safeguarding sensitive data and maintaining operational resilience. This guide delves into the multifaceted world of cloud security, exploring its core components, prevalent threats, and effective mitigation strategies. We’ll examine various architectural approaches, compare leading providers, and discuss best practices for implementation and ongoing management.
From data encryption and access control to incident response and emerging threats like AI-driven attacks, we’ll cover the essential aspects of securing your cloud infrastructure. We’ll also contrast cloud security with on-premise solutions, highlighting the unique challenges and advantages of each approach. By the end, you’ll possess a clearer understanding of how to navigate the evolving landscape of cloud security and protect your valuable assets.
Defining Cloud Security Solutions

Cloud security solutions encompass the technologies, processes, and practices designed to protect data, applications, and infrastructure residing in the cloud. They aim to mitigate risks associated with the unique characteristics of cloud environments, offering a comprehensive approach to safeguarding sensitive information and ensuring business continuity. Effective cloud security is not a single product but a layered strategy.
Core Components of Cloud Security Solutions
A robust cloud security solution typically integrates several key components. These include identity and access management (IAM) systems for controlling user access, data loss prevention (DLP) tools to prevent sensitive information from leaving the cloud environment, security information and event management (SIEM) systems for monitoring and analyzing security events, intrusion detection and prevention systems (IDPS) to identify and block malicious activity, and encryption technologies to protect data both in transit and at rest.
Vulnerability management and regular security assessments are also crucial components, ensuring proactive identification and remediation of weaknesses. Finally, robust incident response plans are essential to effectively manage and recover from security breaches.
Types of Cloud Security Threats
Cloud environments face a diverse range of threats. Data breaches, resulting from unauthorized access or compromised credentials, pose a significant risk. Malware infections, often delivered through phishing attacks or vulnerabilities in applications, can disrupt operations and compromise data integrity. Denial-of-service (DoS) attacks can overwhelm cloud resources, rendering applications and services unavailable. Insider threats, from malicious or negligent employees, represent another critical concern.
Misconfigurations, whether accidental or intentional, can expose sensitive data or create vulnerabilities. Finally, account hijacking, where attackers gain control of user accounts, allows them to access sensitive data and resources.
Examples of Cloud Security Architectures
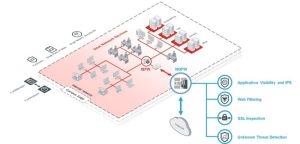
Several architectural approaches can enhance cloud security. A common approach is a layered security model, where multiple security controls are implemented at different layers of the cloud infrastructure. This includes network security (firewalls, intrusion detection), host-based security (antivirus, endpoint detection and response), and application-level security (web application firewalls, input validation). Another approach utilizes a zero-trust model, which assumes no implicit trust and verifies every access request, regardless of its origin.
Microservices architectures, with their inherent isolation and independent deployment, can also improve security by limiting the impact of breaches. Finally, a well-defined security perimeter, coupled with strong access controls and regular security audits, contributes to a robust security posture.
Comparison of Cloud Security Providers
| Provider Name | Key Features | Pricing Model | Customer Support |
|---|---|---|---|
| AWS Security Hub | Security posture management, threat detection, compliance automation | Pay-as-you-go, based on usage | Comprehensive documentation, support forums, and professional services |
| Azure Security Center | Vulnerability management, threat protection, regulatory compliance | Pay-as-you-go, based on resources protected | 24/7 support, online documentation, and community forums |
| Google Cloud Security Command Center | Unified security management, threat detection, vulnerability management | Pay-as-you-go, based on usage | Extensive documentation, support channels, and professional services |
| CrowdStrike Falcon | Endpoint protection, threat intelligence, incident response | Subscription-based, per device or user | 24/7 support, online resources, and dedicated account managers |
Securing your cloud environment requires a proactive and multi-layered approach. This guide has explored the fundamental aspects of cloud security solutions, from defining core components and identifying threats to implementing robust security measures and managing risks effectively. By understanding the key features, comparing different providers, and staying informed about emerging trends, businesses can significantly reduce their vulnerability to cyberattacks and ensure the long-term protection of their data and operations.
The ongoing evolution of cloud technology necessitates continuous vigilance and adaptation to maintain a strong security posture.
Expert Answers
What are the common types of cloud security breaches?
Common breaches include data breaches, denial-of-service attacks, malware infections, insider threats, and misconfigurations.
How much does cloud security typically cost?
Costs vary greatly depending on the size of the organization, the chosen provider, and the level of security required. It can range from a few hundred dollars per month to tens of thousands.
What is the role of compliance in cloud security?
Compliance with industry regulations (e.g., HIPAA, GDPR, PCI DSS) is crucial for maintaining security and avoiding legal penalties. Cloud providers often assist with compliance efforts.
How can I ensure my cloud data is backed up and recoverable?
Implement regular data backups to multiple locations, utilizing cloud-native backup services or third-party solutions. Test recovery procedures regularly.