The digital landscape is constantly evolving, presenting increasingly sophisticated threats to organizational security. Traditional firewalls, while effective in their time, struggle to keep pace with the complexity of modern cyberattacks. This is where Next-Generation Firewalls (NGFWs) step in, offering a robust and adaptable defense against a wide spectrum of threats. NGFWs leverage advanced technologies to provide unparalleled protection, moving beyond simple packet filtering to encompass deep inspection and proactive threat mitigation.
This exploration delves into the core functionalities of NGFWs, their advanced threat protection capabilities, and seamless integration with other cybersecurity solutions. We’ll examine deployment strategies, management best practices, and the future direction of this critical security technology, considering the impact of emerging trends like AI and cloud computing. Finally, we’ll explore broader cybersecurity strategies and present real-world examples of successful NGFW implementations.
Defining Next-Generation Firewall (NGFW) Solutions
Next-Generation Firewalls (NGFWs) represent a significant advancement over traditional firewalls, offering a more comprehensive and adaptable approach to network security. They move beyond simple packet filtering to incorporate advanced threat detection and prevention capabilities, addressing the complexities of modern network environments and sophisticated cyberattacks.NGFWs offer a multi-layered security approach, unlike traditional firewalls which primarily focus on blocking traffic based on IP addresses and ports.
This enhanced functionality allows for more granular control and significantly improved protection against evolving threats.
Core Functionalities of NGFWs
NGFWs integrate multiple security functions into a single platform, streamlining network security management and improving overall effectiveness. These functions extend beyond the basic packet filtering of traditional firewalls to include deep packet inspection, application control, intrusion prevention, and often, advanced threat protection features such as sandboxing and malware analysis. This integrated approach provides a more holistic defense against a wider range of threats.
Key Features of NGFWs
Deep packet inspection (DPI) is a core component of NGFWs. Unlike traditional firewalls that examine only the header information of network packets, DPI analyzes the entire packet payload, identifying malicious content and applications, even those attempting to evade detection through encryption or obfuscation. Application control allows administrators to define granular policies for specific applications, blocking or restricting access based on their risk profile.
Intrusion prevention systems (IPS) monitor network traffic for malicious activity, identifying and blocking known attack signatures and patterns in real-time. These features work in concert to provide a robust defense against various attack vectors.
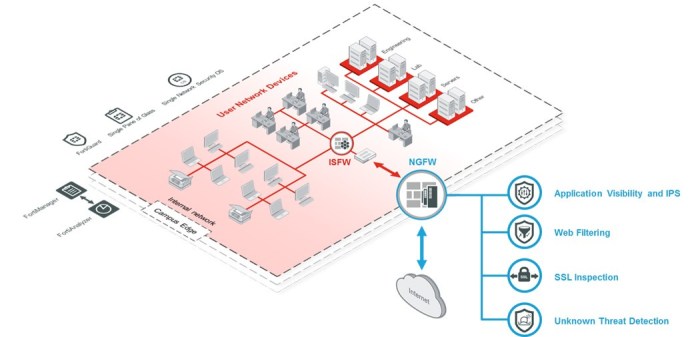
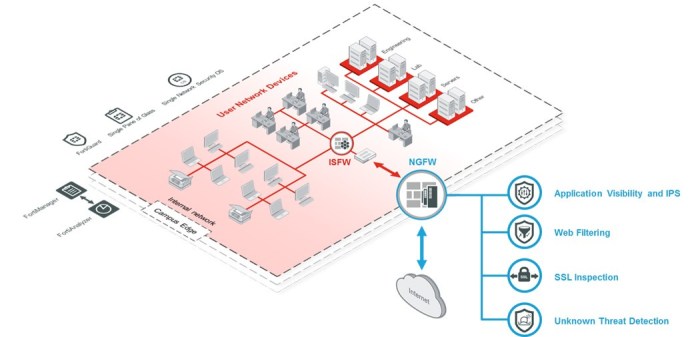
NGFW Deployment Scenarios
NGFWs are deployed across a variety of organizational contexts, adapting to the specific security needs of each environment. For example, in a small business setting, an NGFW might be deployed as a single point of security, protecting all network traffic entering and leaving the organization. Larger enterprises often deploy NGFWs at multiple points in their network, creating a layered security architecture.
In cloud environments, virtualized NGFWs provide similar protection for virtual machines and cloud-based applications. Furthermore, many organizations integrate NGFWs with other security tools, such as Security Information and Event Management (SIEM) systems, to provide a comprehensive security posture. The versatility of NGFWs makes them suitable for a wide array of network topologies and security requirements.
Advanced Threat Protection Capabilities of NGFWs
Next-Generation Firewalls (NGFWs) represent a significant advancement in network security, moving beyond basic packet filtering to offer comprehensive protection against sophisticated threats. Their advanced threat protection capabilities are crucial in today’s complex threat landscape, where traditional firewalls often fall short. This section details how NGFWs mitigate advanced persistent threats (APTs), handle zero-day exploits, and utilize diverse approaches to threat detection and prevention.NGFWs play a vital role in mitigating advanced persistent threats (APTs).
APTs are characterized by their stealthy nature, long-term persistence within a network, and the use of advanced techniques to evade detection. NGFWs combat APTs through several key mechanisms, including deep packet inspection, malware analysis, and intrusion prevention. By analyzing network traffic for malicious patterns and signatures, NGFWs can identify and block APT activities before they cause significant damage. The integration of threat intelligence feeds further enhances their effectiveness, allowing them to proactively identify and neutralize known APT tactics and techniques.
NGFW Effectiveness Against Zero-Day Exploits and Malware
Zero-day exploits and novel malware pose a considerable challenge to traditional security measures. NGFWs address this challenge through advanced techniques like sandboxing and behavioral analysis. Sandboxing involves isolating suspicious files or code in a virtual environment to observe their behavior without exposing the network to potential harm. Behavioral analysis monitors the activity of processes and applications, identifying anomalies that may indicate malicious activity.
This proactive approach helps NGFWs effectively detect and block zero-day exploits and previously unknown malware before they can cause damage. For example, an NGFW might detect a previously unseen piece of malware attempting to establish a connection to a known command-and-control server, triggering an immediate block.
Comparison of NGFW Threat Detection and Prevention Approaches
Different NGFW vendors employ various approaches to threat detection and prevention. Some rely heavily on signature-based detection, identifying known threats based on their unique characteristics. Others leverage machine learning algorithms to analyze network traffic patterns and identify anomalies that might indicate malicious activity, even in the absence of known signatures. A third approach integrates threat intelligence feeds, leveraging information from security researchers and threat intelligence platforms to proactively identify and mitigate emerging threats.
Each approach has its strengths and weaknesses; signature-based detection is effective against known threats but may miss novel attacks, while machine learning approaches can detect unknown threats but may generate false positives. A hybrid approach, combining signature-based detection, machine learning, and threat intelligence, is generally considered the most effective.
Hypothetical NGFW Architecture with Multiple Security Layers
A robust NGFW architecture should incorporate multiple layers of security to provide comprehensive protection. This could include: (1) a perimeter firewall acting as the first line of defense, blocking unauthorized access to the network; (2) an intrusion prevention system (IPS) to detect and block malicious traffic patterns; (3) a web application firewall (WAF) to protect web applications from attacks; (4) a sandbox environment for analyzing suspicious files; (5) a threat intelligence platform to provide up-to-date information on emerging threats; and (6) a security information and event management (SIEM) system to collect and analyze security logs from various sources.
These layers work in concert to provide a multi-faceted defense against a wide range of threats. The integration of these components allows for a comprehensive and layered security approach, ensuring that even if one layer is compromised, others remain in place to provide protection. The effectiveness of this architecture relies on the seamless integration and communication between each layer, enabling a cohesive and responsive security posture.
NGFW Integration with Other Cybersecurity Solutions
Integrating a next-generation firewall (NGFW) effectively into your existing cybersecurity infrastructure is crucial for maximizing its protective capabilities and achieving a robust security posture. A siloed NGFW, operating independently, offers only limited protection. Synergistic integration with other security tools creates a layered defense that significantly improves threat detection, response, and overall resilience. This section will explore best practices for such integration and the resulting benefits.NGFWs enhance overall security posture through integrated threat intelligence sharing and coordinated responses.
When an NGFW detects a suspicious activity, it can immediately correlate this information with data from other security tools, leading to faster and more accurate threat identification and mitigation. This collaborative approach is significantly more effective than relying on individual security tools operating in isolation.
Best Practices for NGFW Integration
Effective integration requires careful planning and execution. Key considerations include standardized logging formats for easier correlation across tools, well-defined communication protocols, and a robust security information and event management (SIEM) system to centralize and analyze security data from various sources. Furthermore, regular testing and validation of the integrated system are vital to ensure its continued effectiveness. The use of APIs (Application Programming Interfaces) is essential for automated data exchange and streamlined workflows.
This minimizes manual intervention and reduces the risk of human error.
Integration Methods: Benefits and Drawbacks
| Integration Method | Benefits | Drawbacks | Example Use Case |
|---|---|---|---|
| API Integration | Automated data exchange, real-time threat intelligence sharing, improved efficiency. | Requires technical expertise for setup and maintenance; potential for API vulnerabilities. | NGFW automatically blocks traffic identified as malicious by an external threat intelligence feed via API. |
| Syslog Integration | Simple to implement; provides centralized logging for security event monitoring. | Limited real-time capabilities; requires manual analysis of log data; potential for log overload. | NGFW sends security logs to a SIEM system for centralized monitoring and analysis. |
| Protocol-based Integration (e.g., SNMP) | Established standards; provides basic device status and performance information. | Limited data exchange; not suitable for real-time threat response; can be complex to configure. | NGFW sends performance metrics (CPU usage, memory usage) to a network management system via SNMP. |
NGFW Enhancement of Overall Security Posture
Integrating an NGFW with other security layers, such as IDS/IPS, SIEM, and EDR solutions, creates a multi-layered defense that significantly strengthens overall security. For example, an IDS/IPS can detect network-based intrusions, while the NGFW can block malicious traffic at the network perimeter. EDR solutions provide endpoint visibility and response capabilities, supplementing the NGFW’s network-level protection. The SIEM system acts as a central hub, correlating security events from all these sources to provide a comprehensive view of the security landscape and facilitate incident response.
This coordinated approach significantly improves threat detection, reduces response times, and enhances overall security resilience. A well-integrated system allows for automated responses to threats, reducing the burden on security personnel and minimizing the impact of successful attacks.
Next-Generation Firewalls represent a critical evolution in cybersecurity, offering a multi-layered defense against increasingly sophisticated threats. By combining advanced threat detection with seamless integration capabilities, NGFWs significantly enhance an organization’s overall security posture. Understanding their capabilities, deployment strategies, and ongoing management is paramount for organizations seeking to protect their valuable data and maintain operational continuity in today’s dynamic threat environment.
The future of NGFWs is bright, with ongoing advancements in AI and cloud integration promising even greater protection against tomorrow’s cyber threats.
User Queries
What is the difference between a traditional firewall and an NGFW?
Traditional firewalls primarily filter traffic based on IP addresses and ports. NGFWs go beyond this, employing deep packet inspection to analyze application content and identify malicious activity, offering more granular control and threat prevention.
How much does an NGFW typically cost?
The cost varies greatly depending on factors like the vendor, features, scale of deployment, and support services. Expect a range from a few hundred dollars for smaller SMB solutions to tens of thousands for enterprise-grade systems.
Are NGFWs suitable for small businesses?
Yes, many vendors offer NGFW solutions tailored for small and medium-sized businesses (SMBs), providing robust security without the complexity and cost of enterprise-level systems. Cloud-based NGFWs are also a cost-effective option for SMBs.
Can an NGFW replace all other security tools?
While NGFWs provide a strong foundation, they are most effective when integrated with other security tools like IDS/IPS, SIEM, and EDR solutions. A layered security approach is crucial for comprehensive protection.